Secure Dataset Integration for 601602340, 5036250135, 611278026, 652123406, 9294164890, 658222390
Secure dataset integration for identifiers such as 601602340, 5036250135, and others is critical for organizational success. With increasing volumes of sensitive data, the need for effective integration methods becomes paramount. This process requires careful consideration of encryption techniques and access controls. A thorough understanding of the challenges faced in merging data sets can inform best practices. However, the implications of compliance with evolving data protection regulations remain a pressing concern. What strategies will ultimately ensure security and efficiency?
Understanding the Importance of Dataset Integration
Although dataset integration is often regarded as a technical necessity, its significance extends beyond mere convenience, impacting data accuracy, accessibility, and operational efficiency.
Effective integration techniques enhance data quality by consolidating disparate sources, enabling users to derive actionable insights.
As organizations seek operational freedom, the seamless amalgamation of datasets becomes vital, fostering an environment where informed decision-making thrives and innovative solutions emerge.
Key Challenges in Merging Sensitive Data
When merging sensitive data, organizations face a myriad of challenges that can complicate the integration process.
Key issues include ensuring robust data encryption to protect information during transit and storage, as well as establishing stringent access control mechanisms to limit data exposure.
Failure to address these challenges can lead to breaches, compromising data integrity and violating regulatory compliance, ultimately undermining trust.
Best Practices for Secure Data Handling
In order to effectively manage sensitive data, organizations must implement best practices that prioritize security at every stage of data handling.
This includes employing data encryption to protect information, establishing access controls for authorized personnel, and enforcing robust user authentication.
Additionally, secure storage solutions and data anonymization techniques should be utilized, alongside regular risk assessments to identify and mitigate vulnerabilities in data management processes.
Compliance With Data Protection Regulations
Compliance with data protection regulations represents a fundamental component of secure dataset integration. Adhering to established regulatory frameworks ensures that organizations uphold data privacy standards, thereby fostering trust among stakeholders.
Conclusion
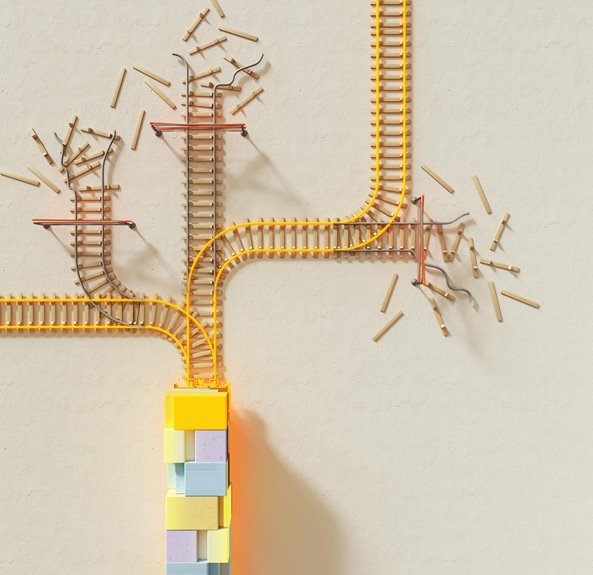
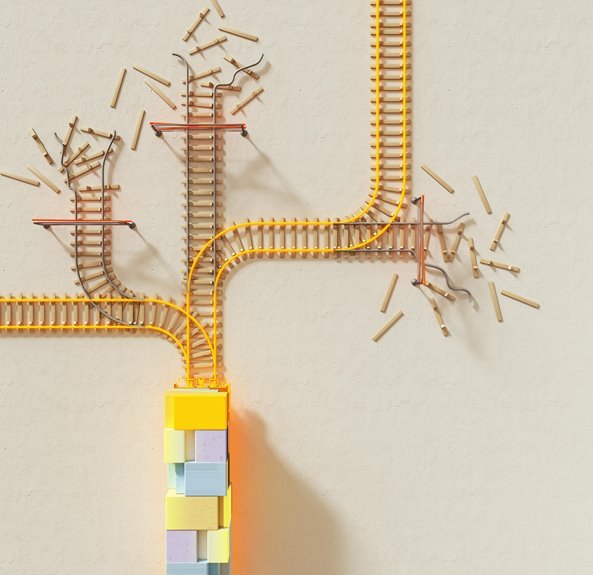
In the pursuit of secure dataset integration for identifiers such as 601602340 and 5036250135, organizations often find themselves navigating a labyrinth of encryption and access controls. Ironically, while the intent is to foster collaboration and trust, the very measures designed to protect sensitive information can sometimes create barriers to seamless data flow. Thus, the challenge remains: achieving a balance between security and accessibility, highlighting the paradox of safeguarding data while simultaneously hindering its utility.